Executive Summary
A hash in blockchain is the cryptographic identifier that compresses a transaction into a unique and verifiable fingerprint. Its real value lies in integrity, since any minimal variation in the data produces a completely different result. That behavior sustains the immutability of the chain by linking each block to the previous one and making any manipulation attempt immediately evident. In practice, the hash turns verification into an automatic and inexpensive process, which is why it is a central piece in transactions, smart contracts, and technical audits.
Introduction: Hash in Blockchain
Understanding what a hash in blockchain is goes beyond academic curiosity, it is the fastest way to grasp why a decentralized network can coordinate without relying on an intermediary. When a transaction is transformed into a digest, the information is not labeled or decorated, it is subjected to a cryptographic function that makes it verifiable in a deterministic way while being extremely sensitive to any alteration. That sensitivity is the mechanism that turns the history of operations into something resistant to forgery, because the system does not debate intentions, it simply detects discrepancies.
The blockchain relies on that property to chain together proofs, not to store faith. Each block incorporates the hash of the previous block and with it inherits its state, so that modifying a detail at any point in the chain means breaking the entire continuity. In a distributed network that break does not go unnoticed, because honest copies compare results and the altered version gets isolated. That is why the hash is not a decorative element of the protocol, it is the mathematical foundation that sustains the security, traceability, and consistency of the ledger.
To ground this without abstraction, this article rests on five critical concepts that explain the real security of the system. The first is the verifiable integrity of the data. The second is the chaining of blocks that sustains the continuity of the ledger. The third is the practical immutability that makes any rewrite costly. The fourth is the irreversibility that prevents reconstructing the data from the digest. And the fifth is secure automation in smart contracts, where the hash stops being theory and becomes execution.
History and Origins of the Hash Function
The idea of summarizing information into a compact identifier first appears as a data engineering need, not as an invention for cryptocurrencies. In the 1950s and 1960s, with mainframes and the first mass processing systems, the priority was to locate records quickly and reduce the cost of comparing large volumes of information. In that context, the hash function is understood as an indexing and classification technique, capable of transforming variable inputs into fixed-size outputs to accelerate searches and verifications. That phase explains why hashing exists in programming and databases even when no cryptography is involved.
The turning point comes when cryptography adopts that same mechanism and turns it into an integrity standard. The hash stops serving only to find data and starts serving to prove that it has not changed, and that shift demands much stricter properties. That is why criteria such as one-wayness, the avalanche effect, and different notions of preimage and collision resistance are formalized, which ultimately determine which algorithms are acceptable in systems where the digest is signed instead of the full document.
In the 1990s, the use of digests becomes widespread and names emerge that become synonymous with cryptographic summaries in software, especially MD5 and later SHA-1, because their performance was practical and their implementation became ubiquitous. Over time, the focus shifted from speed to real security against collisions, and the industry began migrating toward more robust families such as SHA-2 and broadening the range with SHA-3 to reduce dependence on a single design. This historical stretch is not technical nostalgia, it is context for understanding why a blockchain needs resistant hash functions and why a weakness in the digest translates into systemic risk.
The Verifiable Integrity of Data
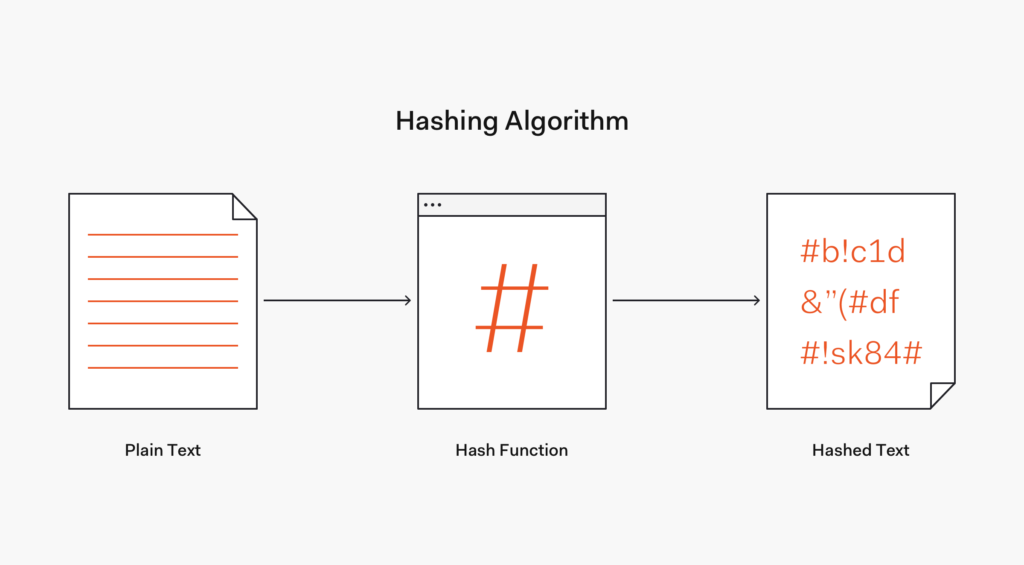
In the blockchain ecosystem, the function of the hash is fundamental for ensuring the integrity and authenticity of transactions. When an operation is initiated, the essential data such as identifiers of the parties, amount, fees, timestamps, and other fields of the format are subjected to a specific cryptographic algorithm. That algorithm generates a fixed-length output that acts as a fingerprint, a summary that represents the content without needing to expose it as readable text or allowing it to be reconstructed.
This digest becomes the technical identifier of the transaction and, in many designs, also the starting point for building proofs or internal references within the block. In practical terms, the network does not need to interpret the transaction to detect changes, it only needs to recalculate the hash and check whether it matches. That is why the process scales, since thousands of nodes can validate consistency with the same calculation without depending on a central server or on trust between participants.
The Chaining Between Blocks
The decisive part happens when that fingerprint is incorporated into the block. Each block groups transactions and also stores the hash of the previous block, creating a direct dependency between the two. That chaining is not a metaphor, it is a mathematical link that breaks when something is modified, because the digest of the block depends on its content and on the references it carries.
Every time a block is added, the chain inherits the previous state through that cryptographic reference. As soon as a relevant byte changes, the hash changes and the block becomes incompatible with the sequence that the rest of the network validates as correct. This is the point that turns a simple accumulation of records into a system with technical memory, where continuity is verified through calculation and not through trust.
The Immutability of the Blockchain and Resistance to Manipulation
The sequential connection of blocks through hashes is not a minor detail, it is the mechanism that turns the ledger into something consistent and verifiable. Each block incorporates the hash of the previous block and inherits its state as a cryptographic reference that certifies that what came before remains intact. If someone attempts to modify the data of a transaction within a specific block, the hash changes completely because hash functions are designed to amplify any minimal variation in the input. That change alters the identity of the block and breaks the continuity with the next one, making the chain no longer fit and the alteration immediately evident.
The practical consequence is that a manipulation cannot be hidden with small adjustments. The altered block stops matching the value that the rest of the nodes expect, because the subsequent block contains an integrity proof of the previous one and that reference no longer points to a valid block. The system can recalculate hashes and confirm whether the sequence of references is consistent, which is why integrity does not depend on human review but on deterministic checks replicated across the entire network.
For an attacker to successfully impose a change, recalculating the digest of the manipulated block would not be enough. They would have to recompute that block and all subsequent ones up to the present, and also do so in a way that their version ends up being accepted as the dominant history. In a decentralized network with multiple synchronized copies, any discrepancy is detected because nodes validate rules and discard versions that do not fit, which makes immutability a practical property based on chaining, distributed verification, and the real cost of rewriting the past.
Hash Irreversibility: Absolute Protection
At the heart of blockchain security and digital transactions lies the property of irreversibility associated with hashes. Irreversibility means that once the data of a transaction is transformed into a hash, there is no practical path to reconstruct the original data from that result. It is not a password lock or a reversible encryption, it is a one-way transformation designed so that the hash functions as a proof of integrity, not as a recoverable container of information. That is why this principle sustains the trust of the system, as it prevents someone from manipulating the record and then trying to cover up the change.
When a hash is generated from transaction data, any modification, even a minimal one, produces a completely different hash thanks to the avalanche effect. That sensitivity turns the hash into an extremely reliable change detector. In addition, irreversibility prevents a reverse attack, because deriving the original content from the hash is not viable except through brute force, and even then the search space is so large that it stops being a realistic option. In blockchain this is key, since the network validates consistency by comparing calculated values, not by interpreting intentions or manually reviewing each operation.
To visualize it, imagine a transaction as a painting and the hash as a high-precision photograph of the complete work. If someone alters a brushstroke, however small, the photograph no longer matches, and that difference appears immediately when the photo is taken again with the same parameters. If someone tried to change the transferred amount, they alter the base data and generate a new hash, but the block where the transaction was stored and the subsequent blocks no longer fit the previous hash. The network detects the discrepancy by recalculating and comparing, and that lack of coincidence acts as an automatic brake against manipulation.
This irreversibility is not just a technical characteristic, it is an operational foundation. By forcing every change to leave a different fingerprint and by preventing the hash from revealing the original content, a double barrier is raised: one against silent alteration and another against extracting information from the digest. In a decentralized environment, where verification occurs across many copies of the chain, that property becomes one of the most powerful drivers of the system’s integrity.
Hashes in Smart Contracts: Secure Automation
The integration of hash functions into smart contracts represents a significant advance in automation and security within the blockchain ecosystem. These contracts, which execute agreements without intermediaries, leverage hashes to fix a verifiable version of critical data and ensure that the contract logic is applied to intact information. In practical terms, the hash acts as a cryptographic fingerprint that allows verifying that a parameter, a document, or a condition has not been altered since it was recorded, which reduces disputes and eliminates opportunistic interpretations.
Within a smart contract there is a constant need to verify and enforce agreed conditions. Hashes come into play by uniquely and securely representing the terms and details of the contract, whether the content of an agreement, the state of a delivery, or the validation of a prerequisite. By generating a hash from those conditions, any alteration produces a drastic change in the digest and the network detects it as an inconsistency. Furthermore, this approach allows working with information commitments without publishing everything in the clear, since the hash can be stored on-chain while keeping the full detail off the blockchain, preserving verifiability without sacrificing privacy or inflating costs.
In contracts with more advanced logic, hashes are also used as a mechanism to coordinate actions between parties without prior trust. They are commonly seen in commit-and-reveal schemes, where a hash is first recorded as a commitment and later the original data is revealed to prove it matches, preventing front-running attacks. Similarly, they appear in mechanisms such as time locks and hash locks, where the fulfillment of a condition depends on presenting a correct preimage within a deadline, enabling conditional exchanges and payments with technical security, not promises.
Practical Examples
In identity verification, a contract can validate attributes without exposing them openly, storing hashes of credentials or proofs and allowing the interested party to demonstrate correspondence when needed. In payment conditions, the hash of the amount, recipient, and conditions is recorded, and the contract automatically releases funds when the requirements are met, ensuring automatic execution without human intervention. In supply chain management, hashes can represent shipping states, provenance, and timestamps, and any variation is flagged, reinforcing traceability and end-to-end integrity.
The history and application of hash functions in blockchain reveals an essential tool that has evolved to sustain the security, integrity, and efficiency of digital transactions.
Conclusion
The hash is the component that most quickly separates a serious blockchain from a database with marketing. Its value does not lie in sounding cryptic, it lies in turning integrity into a verifiable, repeatable, and inexpensive fact. When a transaction is reduced to a fingerprint, the system no longer needs to trust narratives, it only needs to recalculate and compare, and that difference is what allows thousands of nodes to coordinate a shared history without a central arbiter.
The chaining of blocks through hash references is the bridge that transforms local verification into global coherence. Each block inherits the previous state and fixes it with a cryptographic dependency that breaks if the content is touched, which turns any alteration into technical evidence. That continuity is the foundation of practical immutability, because rewriting one part means redoing the rest and also convincing the network to accept that version.
Irreversibility completes the protection because it prevents using the digest as a shortcut to reconstruct sensitive information and forces any manipulation attempt to leave inevitable traces. This makes it possible to prove that something existed in a specific state at a given moment without exposing the full content on-chain, and opens a realistic path to combining transparency with operational privacy.
When smart contracts enter the picture, the hash stops being just security and becomes automation with guarantees. It allows fixing verifiable conditions, coordinating trustless exchanges, and reducing friction in processes where intermediaries and endless reconciliations once prevailed. The correct reading is simple: mastering hashes is not about memorizing definitions, it is about understanding the five concepts that sustain the real security of the ledger.
Frequently Asked Questions
What is a hash in blockchain and what is it for?
A hash in blockchain is a cryptographic fingerprint that summarizes a transaction or a block into a unique and verifiable identifier. It serves to verify the integrity of data without needing to read or interpret it, because it is enough to recalculate and compare the result. If someone alters a field, the digest changes and the network detects the mismatch immediately. That is why it sustains technical auditing, traceability, and automated validation in decentralized systems.
Why does a minimal change completely alter the hash?
Because cryptographic hash functions are designed with the avalanche effect, so that a minimal variation in the input causes a completely different output. This behavior prevents a predictable relationship between the original data and the digest, making it difficult to manipulate information without leaving a trace. In blockchain that sensitivity is an operational advantage, since it turns any modification into an evident signal. Verification becomes deterministic and massive because all nodes can check it with the same calculation.
What does it mean for a hash to be irreversible?
It means the process is one-directional and it is not viable to reconstruct the original data from the hash. A digest is not reversible encryption, since it is not designed to recover content but to prove that content has not changed. This property prevents someone from using the result as a shortcut to deduce sensitive information and reinforces integrity because it forces working with verifiable proofs. In blockchain it allows publishing verifiability without necessarily exposing the full content on-chain.
How does the hash help the immutability of the blockchain?
Each block includes the hash of the previous block and that chaining creates a cryptographic continuity that is validated in cascade. If a block is modified, its digest changes and the next block no longer fits, which breaks the chain and exposes the alteration. To impose the change, an attacker would have to recompute the altered block and all subsequent ones up to the present, and also get the network to accept their version. That is why immutability is practical, it is based on distributed verification and the real cost of rewriting the past.
Is a hash the same as a digital signature?
No, a hash is a cryptographic summary and a digital signature is an authentication mechanism based on keys. In practice, many systems sign the digest of a message instead of the full message because it is more efficient and keeps verification consistent. The hash provides integrity, since it detects changes, while the signature provides authenticity, since it links the message to a sender with a private key. In blockchain both coexist, but they fulfill different roles within the security model.
What role does the hash play inside smart contracts?
The hash allows fixing parameters and states of a contract as an integrity proof that the network can verify without ambiguity. It is used for commit-and-reveal commitments, for validating conditions without publishing full data, and for reducing disputes because any change alters the digest. It also appears in conditional execution schemes, where presenting a correct preimage activates a programmed action within the contract. Together, it turns automation into something trustworthy because it relies on cryptographic verification, not on promises between parties.